In the world of technology, where innovation thrives and digital solutions evolve at breakneck speed, delivering regulated products requires more than just cutting-edge design. It demands a vigilant approach to security, particularly for businesses navigating the complex web of compliance requirements. For organizations across various sectors, maintaining the integrity of regulated products is more crucial than ever before, especially with the increasing sophistication of cyber threats.
Understanding the Landscape of Regulated Products
Navigating Compliance Requirements
The journey of bringing a regulated product to market can feel like a high-stakes endeavor, akin to walking a tightrope without a net. Companies must prioritize compliance with governmental and industry-specific regulations, from the FDA in the United States to various data protection directives in Europe. These frameworks ensure products are not only safe for use but also secure against unauthorized access.
Failing to comply can have dire consequences including legal penalties, reputational damage, and financial losses. Enterprises must build a robust compliance strategy, integrating risk assessments and data protection mechanisms into their product development lifecycle.
Common Challenges Faced
Despite the best efforts, businesses often encounter roadblocks when delivering regulated products. Overcoming these challenges demands a proactive stance on security and collaboration with experienced partners. One significant hurdle is keeping up with the fast-changing regulatory landscape. Companies often struggle to align their operational practices with new compliance standards, especially when they involve intricate technical adjustments.
Another pervasive challenge is ensuring that the development teams are equipped with up-to-date knowledge and tools to implement security measures effectively. This requires continuous training and periodic audits to maintain high levels of security awareness and enforce best practices dedicated to regulated product delivery.
Implementing Security-First Practices
Integrating Security from Inception
Embedding security within the DNA of product development from day one can mitigate potential risks significantly. By adopting a security-first mindset, businesses can weave cybersecurity measures into the early stages of product ideation and design, rather than considering them as an afterthought. This proactive approach ensures that risk identification and mitigation are integral parts of the entire development process.
Integrating security involves conducting threat modeling exercises and security audits, which systematically assess the vulnerabilities that could compromise product integrity. These steps not only bolster defenses but also empower teams to anticipate potential compliance violations and address them before they evolve into critical issues.
Leveraging Strategic Partnerships
Partnering with organizations like KAL Solutions Group can be a strategic move for businesses aiming to enhance their security-first practices. KAL Solutions, with its global network of expert partners, offers services ranging from outsourcing software development to providing Cybersecurity and Compliance Solutions. This broad spectrum of offerings equips companies with the resources and expertise needed to navigate the intricacies of security for regulated products.
Additionally, KAL Solutions’ approach emphasizes scalable development, privacy, and cybersecurity, enabling businesses to accelerate growth safely and effectively. By leveraging their wealth of experience, companies can tap into cutting-edge security practices while maintaining compliance with industry standards.
The Role of Technology and Innovation
Harnessing Advanced Technologies
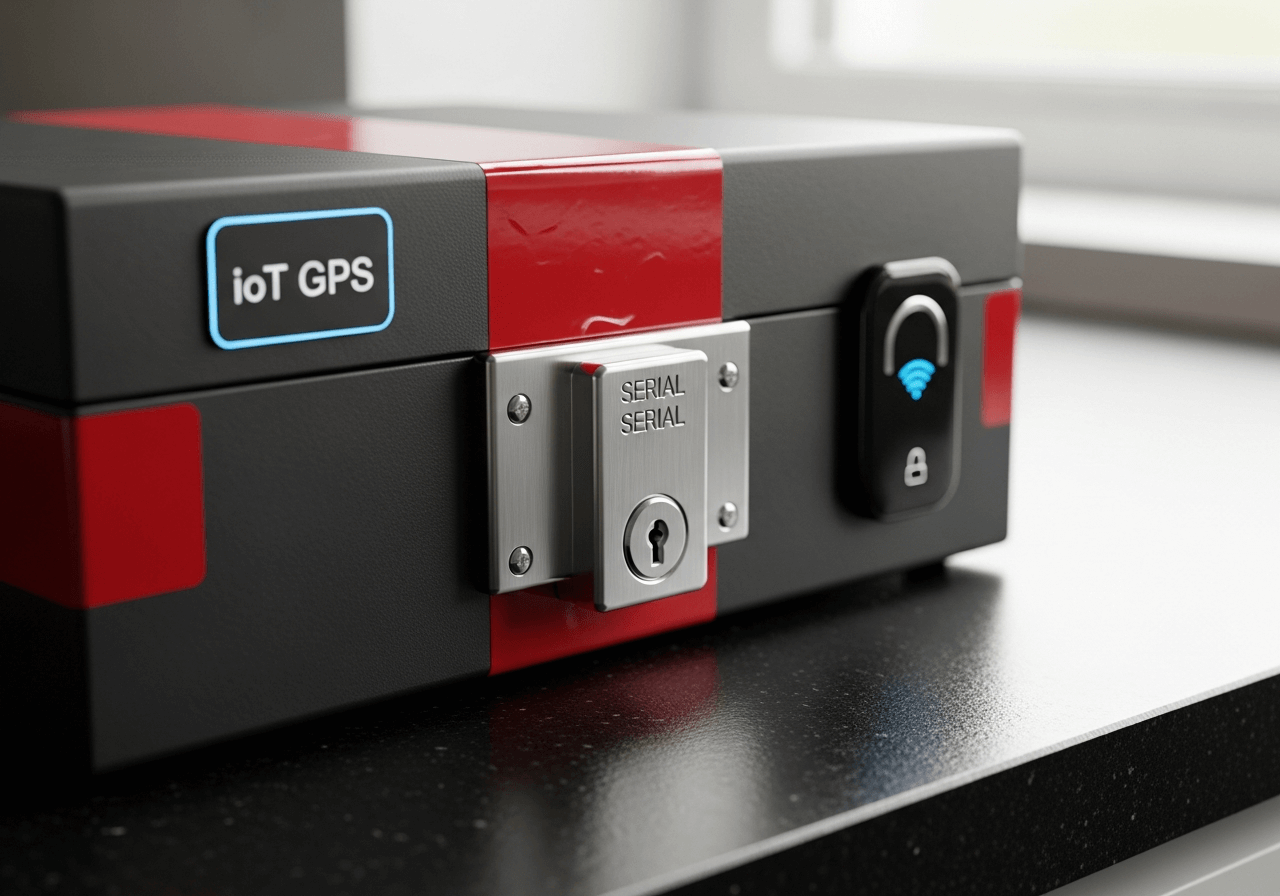
Technology is the backbone of security-first delivery practices for regulated products. Companies must embrace innovative solutions, such as encryption technologies, blockchain for traceability, and AI-driven analytics, to enhance their security posture. These technologies have redefined data protection, making it easier for organizations to safeguard sensitive information and ensure compliance with stringent regulations.
Moreover, automated testing and continuous integration systems can help maintain high security standards throughout the product lifecycle. These tools simplify compliance reporting, ensuring that every aspect of product delivery meets established security benchmarks.
Creating a Culture of Security
Fostering a culture of security within an organization can often be the difference between success and failure in delivering regulated products. This culture must permeate every level of the organization, from front-line developers to executive leadership. Encouraging open communication about security risks and promoting accountability ensures that the entire team is aligned with security objectives.
Training sessions, workshops, and regular updates on emerging threats and compliance changes are essential for maintaining a security-first culture. By prioritizing education and engagement, businesses can equip their teams with the knowledge and skills necessary to address security challenges head-on.
Delivering regulated products in today’s digital age demands meticulous attention to security and compliance. Organizations must not only comply with existing regulations but also stay ahead of emerging threats. This entails a collaborative effort among development teams, strategic partners, and cutting-edge technologies to design, implement, and manage robust security-first strategies within the product delivery lifecycle.
By focusing on a comprehensive approach that blends compliance and technical innovation, businesses can effectively unlock opportunities in regulated markets. They can expand their reach, confidently bring new products to market, and fortify their reputation as leaders in security and compliance. The journey may be demanding, but with the right strategies and partnerships, achieving security-focused excellence in regulated product delivery is within reach. As organizations continue to navigate this intricate landscape, the imperative remains clear: prioritize security at every stage to build a resilient and compliant future.